Tar Boom Website
Discover functionality of the website
On the web site nothing relevant, we can only upload a .tar file and he is decompress and save on the website server !
Looking to the code
After looking to the code i see that the file path tar_path is based on the file.name wichi is send by the user in the POST request, and it’s never sanatized or checked.
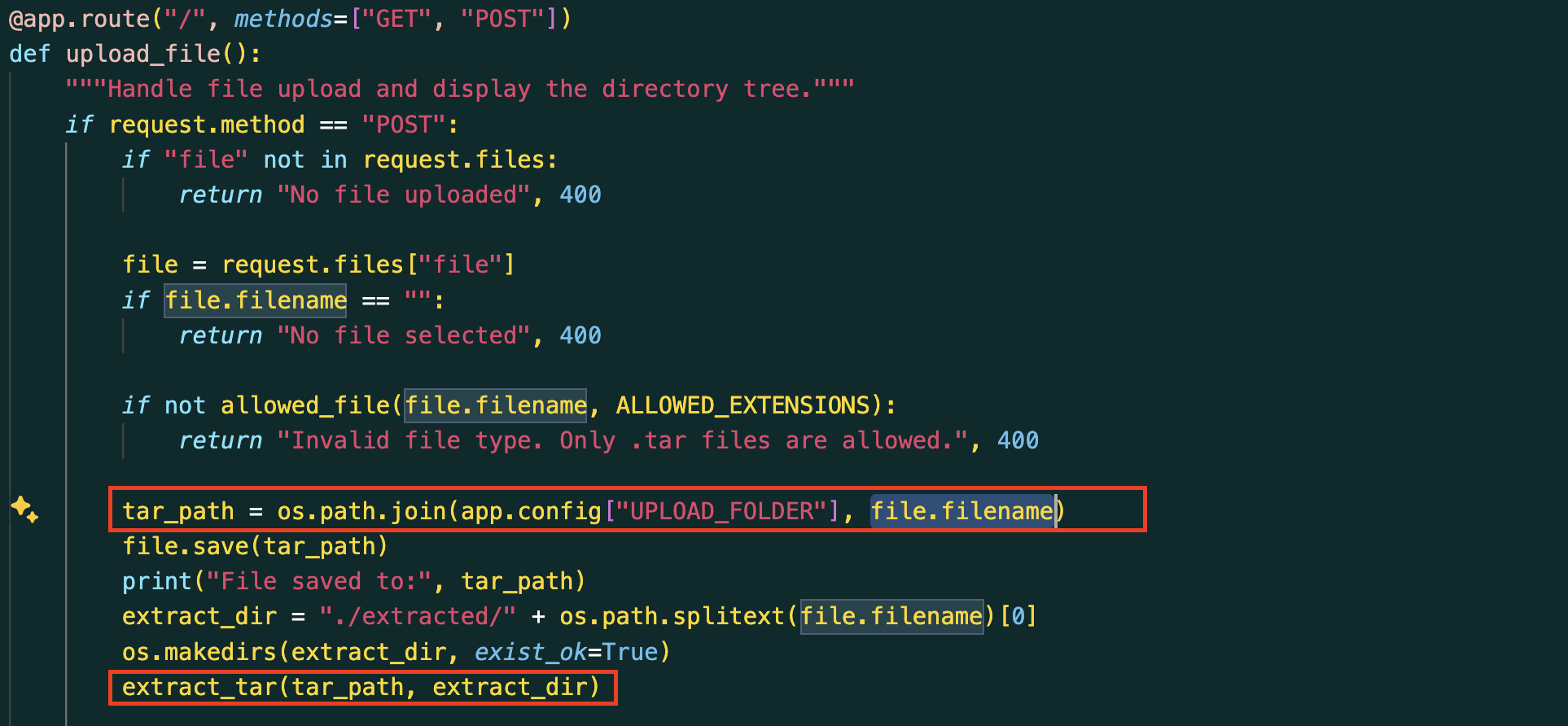
So basically it mean that we can upload a file where we want on the server, with a simple POST request !
1 | POST / HTTP/1.1 |
With this POST request, i just uploaded my file payload.tar to the /path of the server.
How execute my payload ?
At this moment i was wondering, how i could execute the file i uploaded on the server to read the env variable, where the flag is !
I first checked if SSH was open on the instance server, maybe i could copy my public ssh key to the path ~/.ssh/authorized_keys and get an ssh access the get the flag ?
But nop ^^ ssh wasn’t enable …
And then i remember that server was executing a server side template to print the extracted file for the user !
What will happen if i try to over write the template result.html file ?
Switch filename to templates.tar, because the file result.html with is the loaded file to print the result is in ../templates, and named the file result.html to over write the original one
1 | POST / HTTP/1.1 |
And that was working, i get a my <h1>SSTI</h1> page !
After i know this was working, i search a payload to print the os environement variables where the flag was.
Found this one :{{config.__class__.__init__.__globals__["os"].environ["FLAG"]}}
The whole payload
1 | POST / HTTP/1.1 |
And we got the flag !!
Really cool challenge thx to DVCTF !
This work is licensed under a Creative Commons Attribution-NonCommercial-ShareAlike 4.0 International License .